Your website is live. Visitors are landing on it. But behind the scenes, hundreds of automated bots and scanners are probing it every single day, looking for anything they can exploit. That is the reality of running a site on the internet, and it is why firewalls are not optional anymore.
If you are new to web hosting or just starting to dig into the security side of things, the word “firewall” can feel like a black box. You know it is important, but nobody seems to explain it in a way that actually makes sense.
This guide does exactly that. You will learn:
- What a firewall actually is and how it works
- The different types of firewalls used in web hosting
- What a Web Application Firewall (WAF) does specifically for websites
- How to configure firewall rules without breaking your site
- Which tools and services are worth using in 2026
- What mistakes to avoid when setting one up for the first time
Whether you are running a personal blog on shared hosting or managing a VPS for a growing business, this guide gives you a solid foundation and enough depth to make informed decisions.
Key Takeaways
- A firewall is a security barrier that filters traffic between the internet and your web server based on rules you define.
- There are multiple types of firewalls, and web hosting environments typically use a combination of them.
- A Web Application Firewall (WAF) is designed specifically for HTTP/HTTPS traffic and protects against attacks like SQL injection and cross-site scripting (XSS).
- Firewalls do not replace other security measures like SSL certificates, software updates, and strong passwords. They work alongside them.
- Most quality hosting providers include at least basic firewall protection, but configuring it properly is still your responsibility.
- According to IBM’s 2025 Cost of a Data Breach Report, the average cost of a data breach globally hit $4.44 million, making proactive protection far cheaper than reactive damage control.
Quick Answer: What Is a Firewall in Web Hosting?
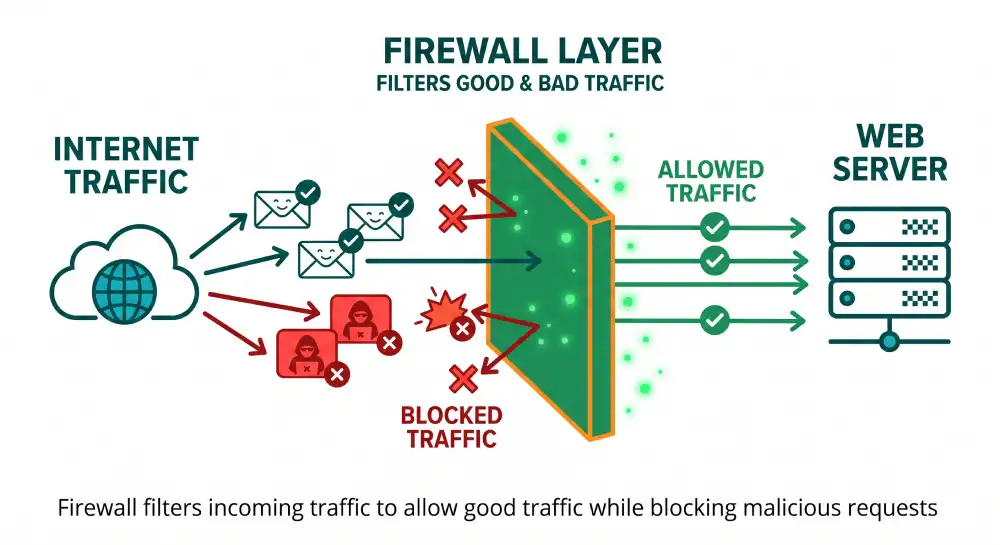
A firewall in web hosting is a security system that monitors and controls all incoming and outgoing traffic to your web server. It uses a set of rules to decide what gets through and what gets blocked. Think of it as a security checkpoint at the entrance to your server. Legitimate visitors pass through; malicious traffic gets turned away at the door.
What Does a Firewall Actually Do?
Before getting into types and configurations, it helps to understand the core job of a firewall.
Every time someone visits your website, a connection request travels from their browser to your web server. That request carries data, such as what page they want, their IP address, and other technical details. A firewall sits between the internet and your server and reads those requests before they reach your site.
Based on the rules you set, it decides:
- Allow the connection through
- Block the connection entirely
- Log it for review without taking immediate action
This happens thousands or even millions of times per day on busy sites. Most of the traffic is legitimate, but a meaningful portion is automated bots running vulnerability scans, brute-force login attempts, or probing for known software weaknesses.
Without a firewall, all of that traffic reaches your server directly. Your server then has to handle it, which wastes resources, slows down your site, and leaves your files and databases exposed to anything with bad intent.
The Different Types of Firewalls You Will Encounter
Not all firewalls work the same way. Each type operates at a different layer of your network and catches different kinds of threats. Here is a breakdown of what each one does in practical terms.
Packet Filtering Firewalls
This is the most basic type. A packet filtering firewall examines individual data packets as they travel to and from your server. It checks things like:
- Source IP address (where the traffic is coming from)
- Destination IP address (where it is going)
- Port numbers (which service is being accessed)
- Protocol type (TCP, UDP, ICMP, etc.)
If a packet matches a blocked rule, it gets dropped. If it does not match anything suspicious, it passes through.
The limitation here is that packet filtering only looks at the envelope, not the letter inside. It can block traffic from a known bad IP address, but it cannot tell whether a packet from a clean IP contains malicious code.
Stateful Inspection Firewalls
Stateful inspection goes a step further. Instead of examining each packet in isolation, it tracks the entire state of a connection.
When your browser opens a connection to a website, a stateful firewall records that connection as active. Any incoming packets that do not match an established, legitimate connection get flagged and dropped. This approach catches more sophisticated attacks that try to sneak in by mimicking legitimate traffic patterns.
Most modern operating system firewalls and server-level firewalls use stateful inspection as a baseline.
Application Layer Firewalls
These firewalls understand specific protocols like HTTP, FTP, or DNS. They can look inside the data payload of a packet and make decisions based on what the application-level content actually says.
For web hosting, this matters a lot. An attacker could send traffic from a perfectly legitimate IP address, on a standard port, using normal HTTP protocols, but the actual request could contain malicious code trying to exploit your login form or database.
Application layer firewalls can detect that.
Web Application Firewalls (WAF)
A WAF is the type most directly relevant to web hosting, and it deserves its own section below. The short version is that a WAF is an application layer firewall built specifically for websites and web applications, monitoring every HTTP and HTTPS request with rules designed to catch web-specific attacks.
Next-Generation Firewalls (NGFW)
NGFWs combine packet filtering, stateful inspection, deep packet inspection (DPI), and application awareness into one system. They can also integrate with threat intelligence feeds to block traffic from known malicious sources in real time.
The NGFW market exceeded $5.4 billion in 2025, which reflects how critical enterprise-grade firewall technology has become. For most small to mid-sized hosting environments, a WAF combined with a good host-level firewall provides solid coverage without the complexity of a full NGFW deployment.
Web Application Firewalls Explained: Your Website’s Dedicated Guard
If you run a website, the WAF is the firewall that matters most to you personally.
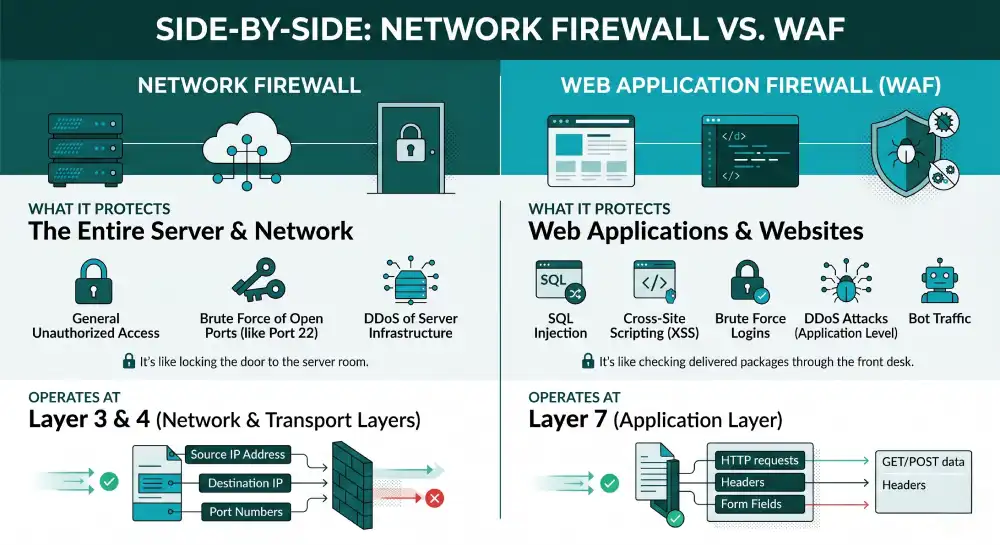
A standard network firewall protects the server itself from unauthorized access. A WAF protects your web application from attacks that travel through legitimate HTTP traffic.
Here is a simple way to think about the difference:
- The network firewall locks the server room door.
- The WAF checks every package delivered through the front desk.
What Attacks Does a WAF Block?
SQL Injection: An attacker enters malicious SQL code into a form field on your site, such as a login box or search bar, hoping the database will execute it and expose sensitive records. A WAF recognizes these patterns and blocks the request.
Cross-Site Scripting (XSS): An attacker injects malicious JavaScript into a web page that then runs in another user’s browser. This can steal session cookies, redirect users to phishing sites, or deface your content. A WAF catches these injection attempts.
Brute Force Attacks: Bots attempt thousands of login combinations per minute trying to guess usernames and passwords. A WAF with rate limiting blocks excessive requests from a single source before they succeed.
DDoS Attacks: Distributed denial-of-service attacks flood your site with traffic to take it offline. WAFs at the edge can absorb or filter this traffic before it reaches your actual server.
Bot Traffic: Not all bots are Google. Many are scrapers, spammers, and vulnerability scanners. A WAF can identify and block non-human traffic based on behavior patterns.
In 2026, advanced WAFs also provide bot mitigation, rate limiting, and protection against brute-force logins as standard features, rather than premium add-ons. You can learn more about how WAFs handle modern threats from Cloudflare’s WAF documentation.
Cloud-Based WAF vs. On-Server WAF
You have two main options for deploying a WAF:
| Type | How It Works | Best For |
|---|---|---|
| Cloud-based WAF | Traffic passes through the WAF provider’s network before reaching your server | Shared hosting, WordPress sites, easy setup |
| On-server WAF (software) | Installed directly on your VPS or dedicated server | VPS/dedicated users who want more control |
| Hardware WAF | Physical device placed in front of your network | Enterprise setups, large data centers |
For most website owners on shared or WordPress hosting, a cloud-based WAF like Cloudflare or Sucuri is the easiest and most effective option. You point your domain’s DNS to the WAF provider, and all traffic routes through them first before reaching your host.
How Firewalls Work Inside Your Hosting Environment
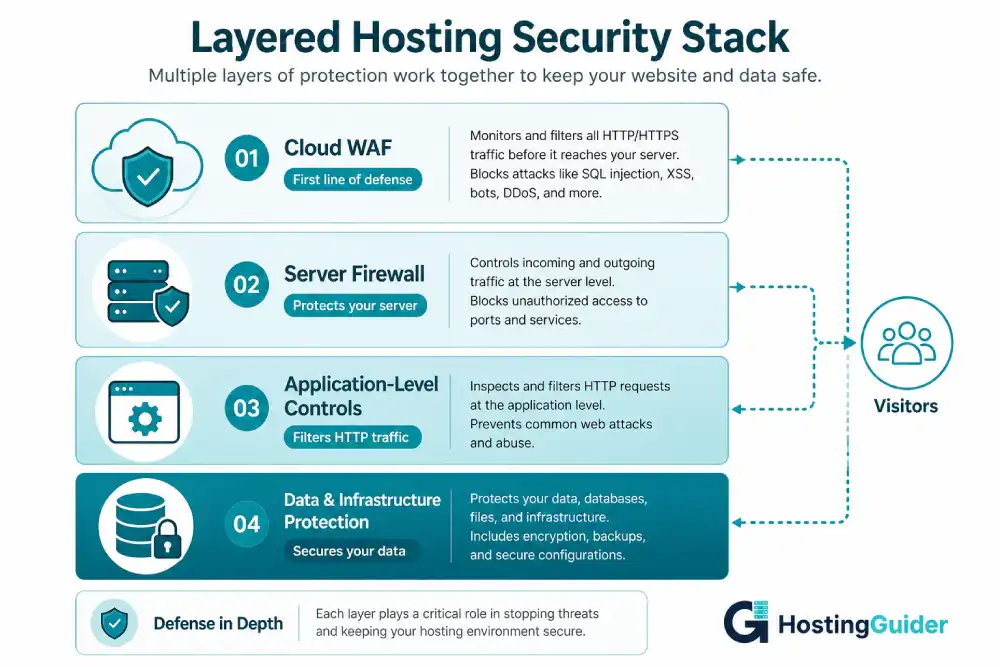
Your hosting environment likely has multiple firewall layers already, even if you are not fully aware of them.
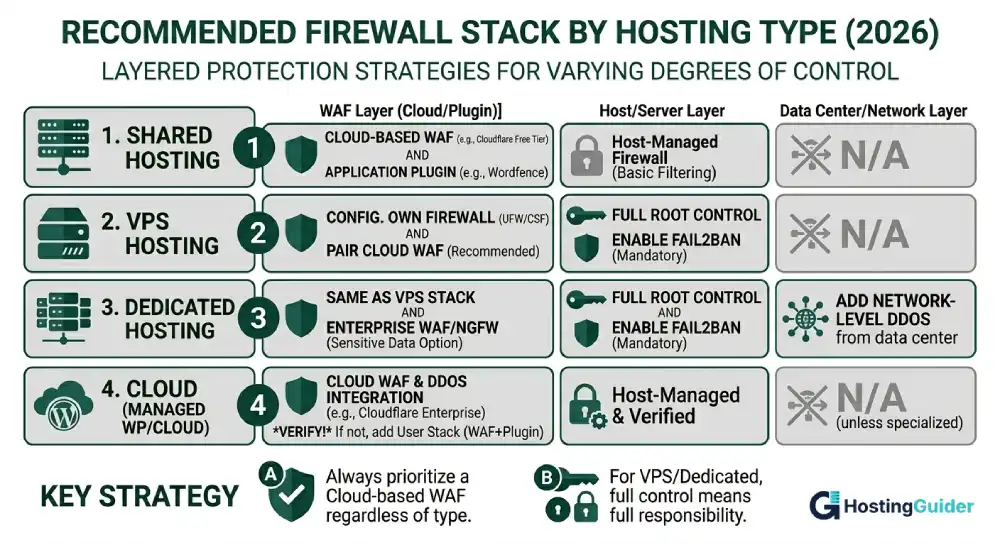
Shared Hosting
On shared hosting, your provider manages the server-level firewall. You share that protection with every other customer on the same server. You typically have little control over the firewall rules at the server level.
What you can control is adding a WAF at the application layer, usually through a plugin (like Wordfence for WordPress) or a DNS-based service like Cloudflare.
VPS Hosting
A VPS gives you root access, which means you can configure your own firewall directly. Common tools include:
- UFW (Uncomplicated Firewall): A user-friendly interface for managing iptables rules on Ubuntu/Debian systems. Good for beginners.
- iptables: The underlying Linux firewall system. More powerful but requires familiarity with command-line rules.
- firewalld: Used on CentOS and RHEL-based systems, offering zone-based firewall management.
- CSF (ConfigServer Security and Firewall): Popular among cPanel VPS users, with a web-based interface and login failure detection built in.
You can also pair any of these with a cloud-based WAF for layered protection.
For a deeper look at how firewall configuration works at the server level, Fortinet’s firewall configuration guide walks through the core concepts clearly.
Dedicated Hosting
Dedicated servers follow the same principles as VPS but give you full hardware control. You have the option to install any firewall software, add hardware firewall appliances upstream, or integrate directly with network-level DDoS protection from your data center.
Setting Up Basic Firewall Rules for Your Website
You do not need to be a systems administrator to get basic firewall rules working on a VPS. Here is a practical starting point for someone using UFW on Ubuntu.
Step 1: Check if UFW is installed
sudo ufw status
Step 2: Set default policies
sudo ufw default deny incoming
sudo ufw default allow outgoing
This blocks all incoming traffic by default and allows outgoing connections.
Step 3: Allow the services you actually need
sudo ufw allow ssh
sudo ufw allow http
sudo ufw allow https
If you use a custom SSH port (which is a good security practice), replace “ssh” with the actual port number.
Step 4: Enable UFW
sudo ufw enable
Step 5: Verify your rules
sudo ufw status verbose
This setup blocks everything that does not match your allowed rules. It is a solid starting point that you can build on as your needs grow.
OWASP’s Top 10 list is worth bookmarking as a reference when you start thinking about which attack vectors your firewall rules should prioritize. It covers the most common web application vulnerabilities updated regularly.
Common Firewall Mistakes Website Owners Make
Knowing what to do is only half the equation. Here are the mistakes that trip up even technically confident users.
Leaving the default SSH port open with no IP restriction Port 22 is the first thing every scanner checks. Either change it to a custom port, restrict it to your IP address only, or both.
Allowing all traffic on port 3306 That is the default MySQL database port. It should never be open to the public internet. If you need remote database access, use an SSH tunnel or restrict it to a specific IP.
Not testing firewall rules after changes A misconfigured rule can lock you out of your own server. Always test in a second terminal window before closing your original session.
Treating a firewall as a complete security solution A firewall is one layer of defense. It does not replace keeping your software updated, using strong passwords, or running malware scans. According to a 2025 PrivacyTrust study, 59% of customers said they would stop doing business with a company after a data breach, which means the real cost of poor security goes well beyond the technical damage.
Ignoring outbound rules Most people only think about blocking inbound threats. But if malware does get onto your server, outbound rules can prevent it from communicating with a remote attacker or spreading to other systems.
Firewall Logs: What They Tell You and Why You Should Read Them
Your firewall generates logs every time it blocks or allows traffic. Most beginners set up a firewall and never look at the logs again. That is a missed opportunity.
Firewall logs show you:
- Which IP addresses are probing your server most aggressively
- What ports attackers are targeting
- Whether your rules are blocking traffic you actually want to allow
- Patterns that suggest a coordinated attack is building up
You do not need to read every line manually. Tools like Fail2Ban automatically scan your logs and temporarily block IPs that trigger repeated failed connection attempts. Combining Fail2Ban with UFW on a Linux VPS gives you automated, adaptive protection that tightens over time.
For a thorough breakdown of how WAFs handle traffic inspection and logging, Kinsta’s firewall guide covers practical scenarios worth reading.
How to Choose the Right Firewall Setup for Your Hosting Type
There is no universal answer here. The right setup depends on what you are hosting, how much control you have, and what your budget looks like.
If you are on shared hosting: You have limited server-level control. Focus on adding a cloud-based WAF (Cloudflare’s free tier is a solid starting point), using a security plugin if you are on WordPress, and enabling two-factor authentication on your hosting control panel.
If you are on a VPS: Configure UFW or firewalld as your server firewall. Add CSF if you use cPanel. Pair that with a cloud WAF for application-layer protection. Enable Fail2Ban for automated threat response.
If you are on dedicated hosting: Do everything in the VPS category, plus explore network-level DDoS protection from your data center. Consider integrating with an enterprise WAF or NGFW if you handle sensitive user data.
If you use managed WordPress hosting: Many managed hosts, including options like Kinsta, include Cloudflare integration with WAF and DDoS protection built in. Verify exactly what your host includes before assuming you are fully covered.
The SiteGround Academy’s website security guide offers a practical checklist worth following once your firewall is in place.
Zero Trust and Firewalls: What Beginners Should Know
You may have heard the phrase “Zero Trust” recently, especially in conversations about modern cybersecurity. It sometimes comes paired with claims that firewalls are obsolete. That is not accurate.
Zero Trust is a security model built around one principle: never assume any user or system is trustworthy by default, even if it is already inside your network. Every access request gets verified, every time.
Firewalls fit naturally into this model. In a Zero Trust setup, a firewall is still the enforcer of access policies. It just works alongside identity verification, device validation, and continuous monitoring rather than acting as the only line of defense.
For website owners, the practical takeaway is simple: combine your firewall with strong authentication, regular access reviews, and principle of least privilege (give each user and service only the permissions they actually need).
FAQ: Firewall Basics for Web Hosting
Do I need a firewall if my hosting provider already includes one?
Yes. Your hosting provider’s server-level firewall protects the shared infrastructure, but it does not monitor your specific web application traffic in detail. Adding a WAF gives you application-layer protection targeted at your site specifically. Think of it as adding a security camera inside the building even though there are already guards at the front door.
What is the difference between a WAF and a regular firewall?
A regular firewall (network firewall) controls traffic at the network level based on IP addresses, ports, and protocols. A WAF specifically inspects HTTP and HTTPS web traffic and blocks attacks that use legitimate web requests as their vector, such as SQL injection or XSS. Both serve different functions and work best when used together.
Can a firewall slow down my website?
A poorly configured or low-quality firewall can add latency. However, well-configured cloud-based WAFs from providers like Cloudflare often improve performance because they also function as a CDN, caching your content closer to your visitors. In practice, a good WAF adds negligible delay and sometimes makes your site faster.
Is Cloudflare’s free plan enough for a small website?
For most small websites, Cloudflare’s free plan provides meaningful protection, including DDoS mitigation, bot filtering, and a basic WAF. As your site grows or if you handle sensitive user data like payment information or login credentials, the paid plans offer more granular rule control and threat analytics.
What ports should I block by default on my VPS?
A safe default is to block all incoming traffic and then explicitly open only what you need. At minimum, allow SSH (on a non-default port if possible), HTTP (port 80), and HTTPS (port 443). Block ports like 3306 (MySQL), 6379 (Redis), and 27017 (MongoDB) from public access entirely.
How do I know if my firewall is actually working?
You can test basic port exposure using online tools like ShieldsUP from Gibson Research or by running an Nmap scan from a separate machine. Check your firewall logs regularly for blocked connections. If you are seeing blocks from known scanner IP ranges, your firewall is doing its job.
Final Thoughts
Firewalls are not complicated once you strip away the jargon. At their core, they are filters that let good traffic through and stop bad traffic at the door.
For web hosting, that means combining a server-level firewall to lock down your infrastructure with a WAF to protect your web application specifically. Together, they form the foundation of a practical security posture that covers most real-world threats.
Start with what you have. If you are on shared hosting, add Cloudflare. If you are on a VPS, configure UFW and add Fail2Ban. As your site grows and your security needs get more specific, layer in more controls.
Security is not a one-time setup. Revisit your firewall rules every few months, keep an eye on your logs, and stay current with the tools and threats relevant to your hosting environment. The investment of a few hours up front protects you from problems that can cost far more in downtime, data loss, and recovery.